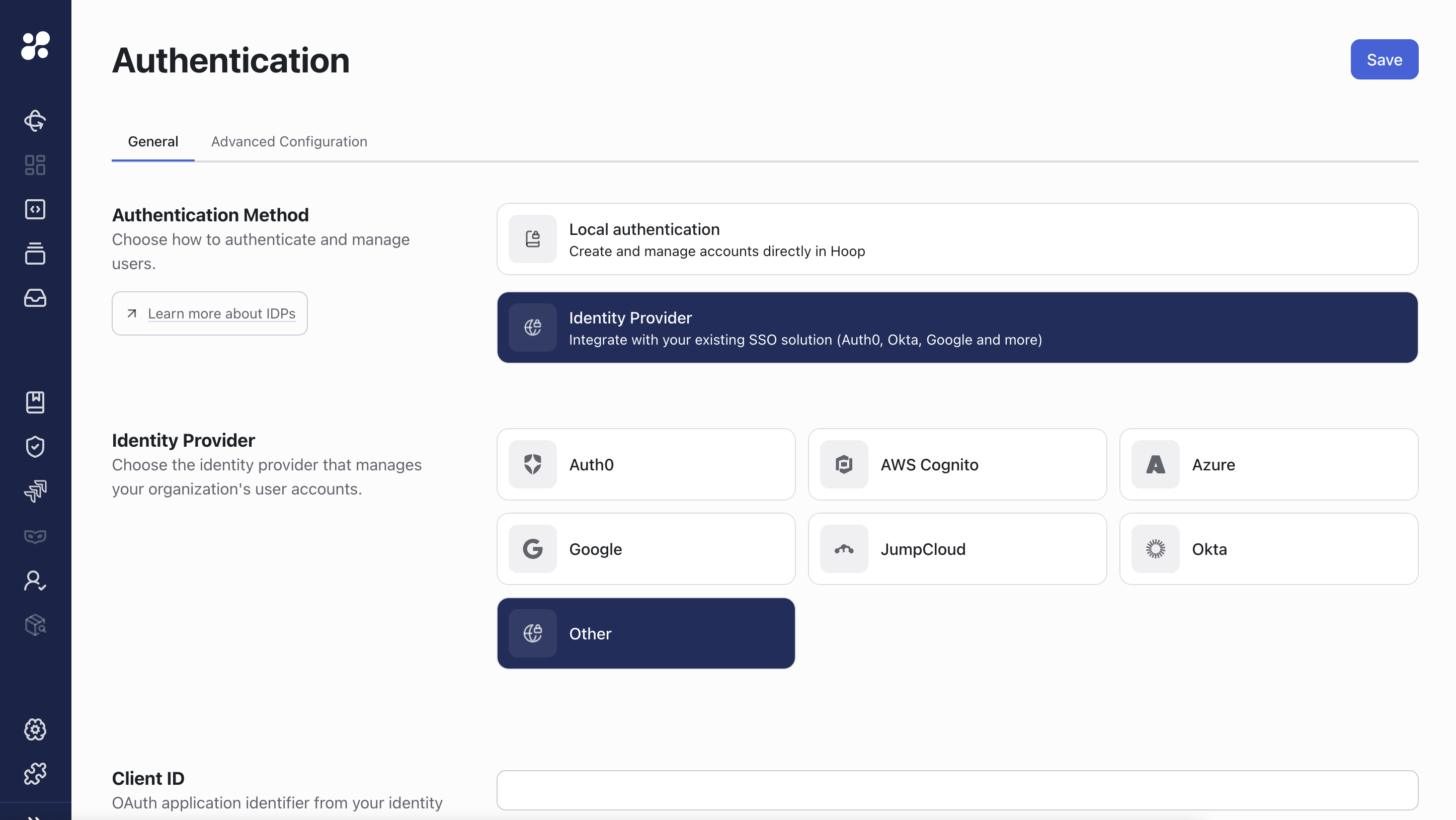
Hoop.dev supports a variety of Identity Providers for user authentication. The guides below cover providers we have validated, but any OIDC-compliant or SAML2.0 IDP should work using the same integration method.Documentation Index
Fetch the complete documentation index at: https://mintlify.hoop.dev/docs/llms.txt
Use this file to discover all available pages before exploring further.
Auth0
Okta
Azure
Jump Cloud
AWS Cognito
OneLogin
Keycloak
Users
Users are active and assigned to the default organization on signup. A user can be set to an inactive state to block platform access, but managing user state in the identity provider is the recommended approach.- The
subclaim is the main user identifier in the platform. - For OIDC, the user profile is derived from the
emailandnameclaims in theid_token. - For SAML, the user profile is derived from assertion Attribute Values
SAML 2.0 Attribute Values
To propagate information from your Identity Provider to Hoop, propagate them via Attribute Values. The supported attributes are described below:Email Address
emailemailaddressmailhttp://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddresshttp://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn
First Name
first_namenamehttp://schemas.microsoft.com/identity/claims/displaynamehttp://schemas.xmlsoap.org/ws/2005/05/identity/claims/namehttp://schemas.xmlsoap.org/ws/2005/05/identity/claims/givenname
Last Name
last_namehttp://schemas.xmlsoap.org/ws/2005/05/identity/claims/surname
Groups
If the SAML Assertion contains an attribute value with the namegroups it will synchronize this attribute on every login.
Groups
Groups define who can access or interact with specific resources:- For resource roles, groups control which users can access a specific resource role. This is enforced when the Access Control feature is enabled.
- For access requests, groups define who can approve an execution. This is enforced when the Access Requests feature is enabled.
Roles
- The admin group grants full access to all resources.
- The auditor group grants read-only access to session resources.
Configuration Page
This feature is available beginning with version
1.38.12