Access Control lets you restrict which users can see and access specific resource roles based on their group memberships. This page covers detailed configuration options.Documentation Index
Fetch the complete documentation index at: https://mintlify.hoop.dev/docs/llms.txt
Use this file to discover all available pages before exploring further.
For an introduction to Access Control concepts, see Access Control Overview.
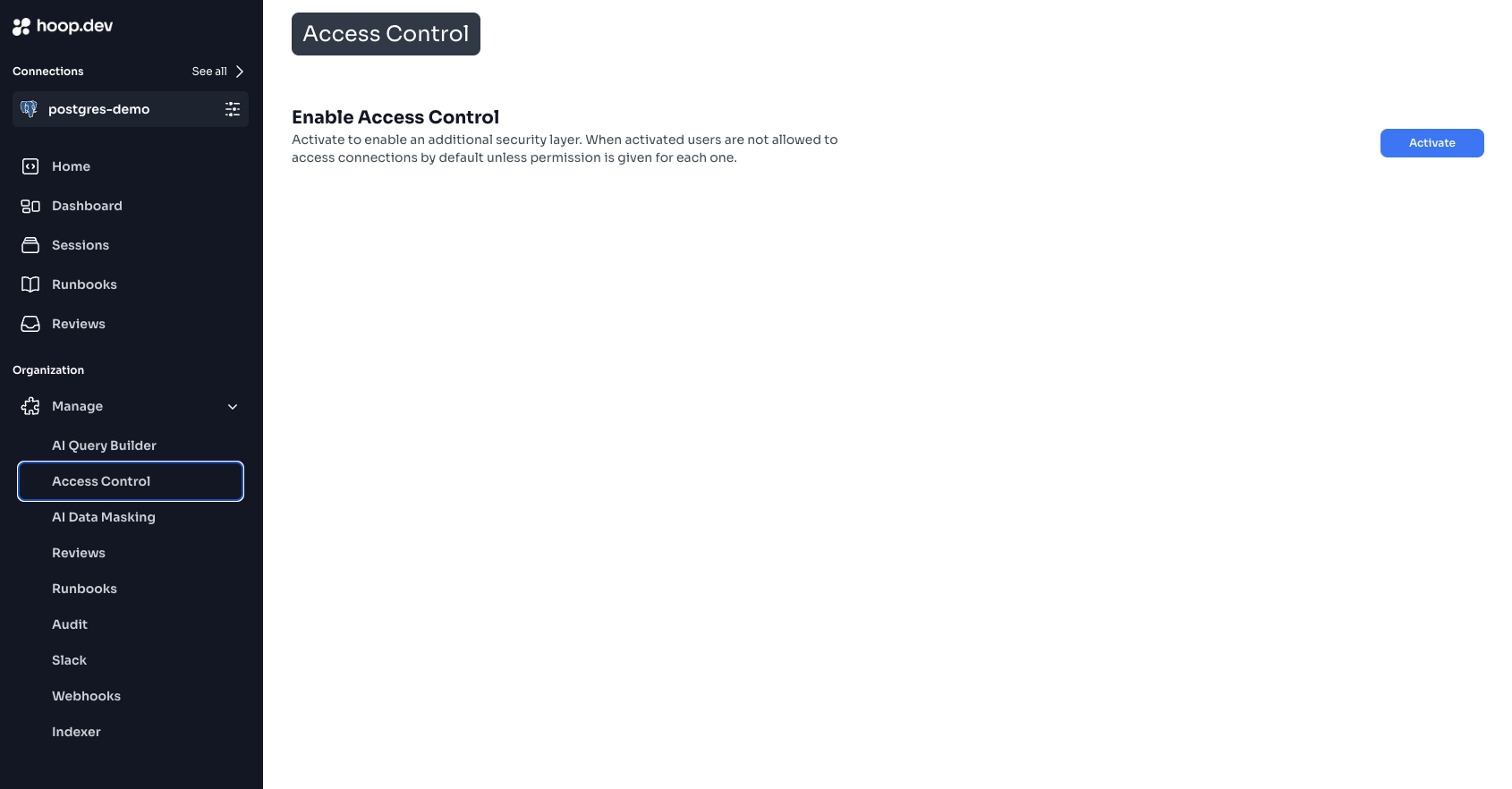
Enabling Access Control
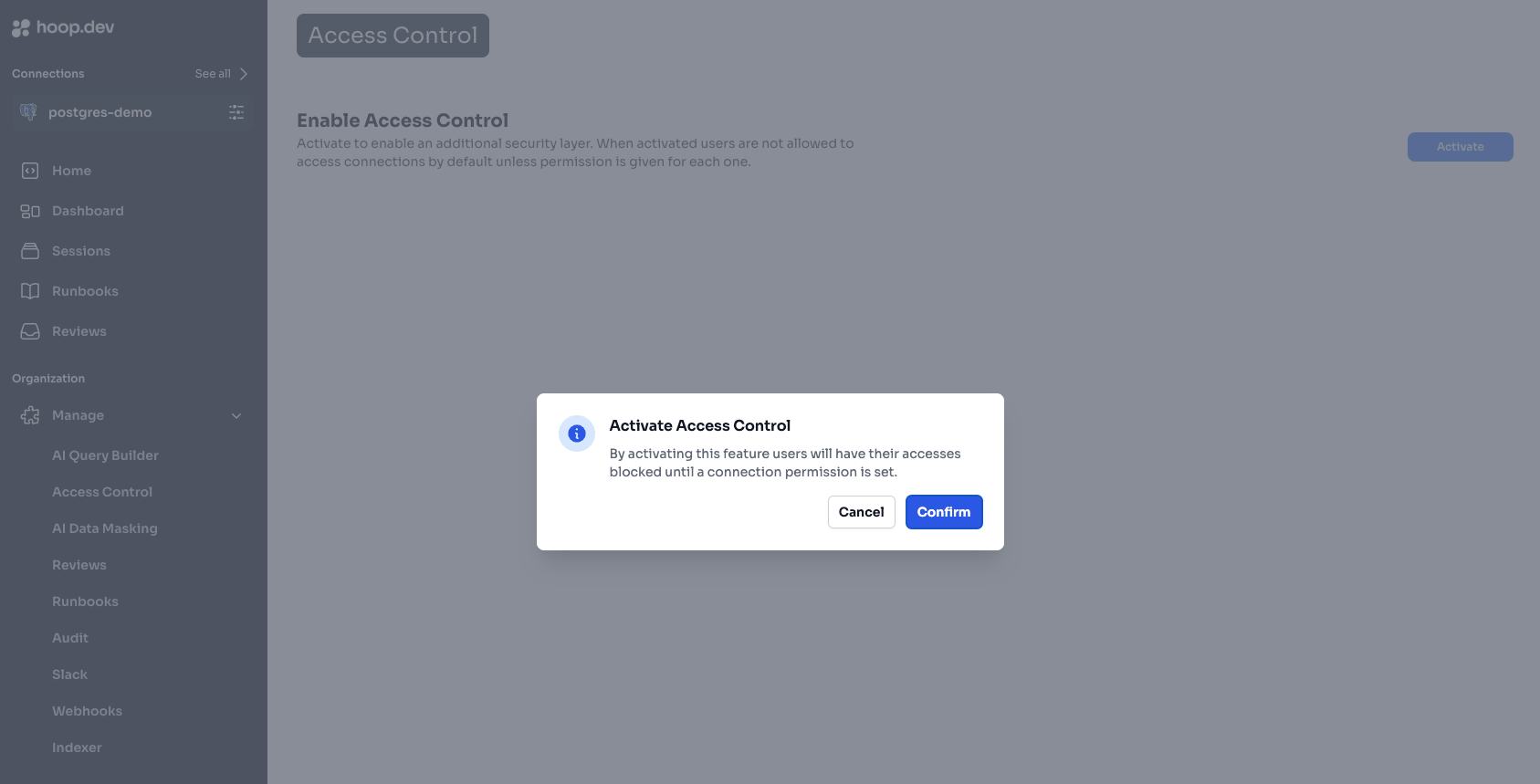
Step 1: Activate Access Control
Review the Warning
Read the activation warning carefully. Understand that: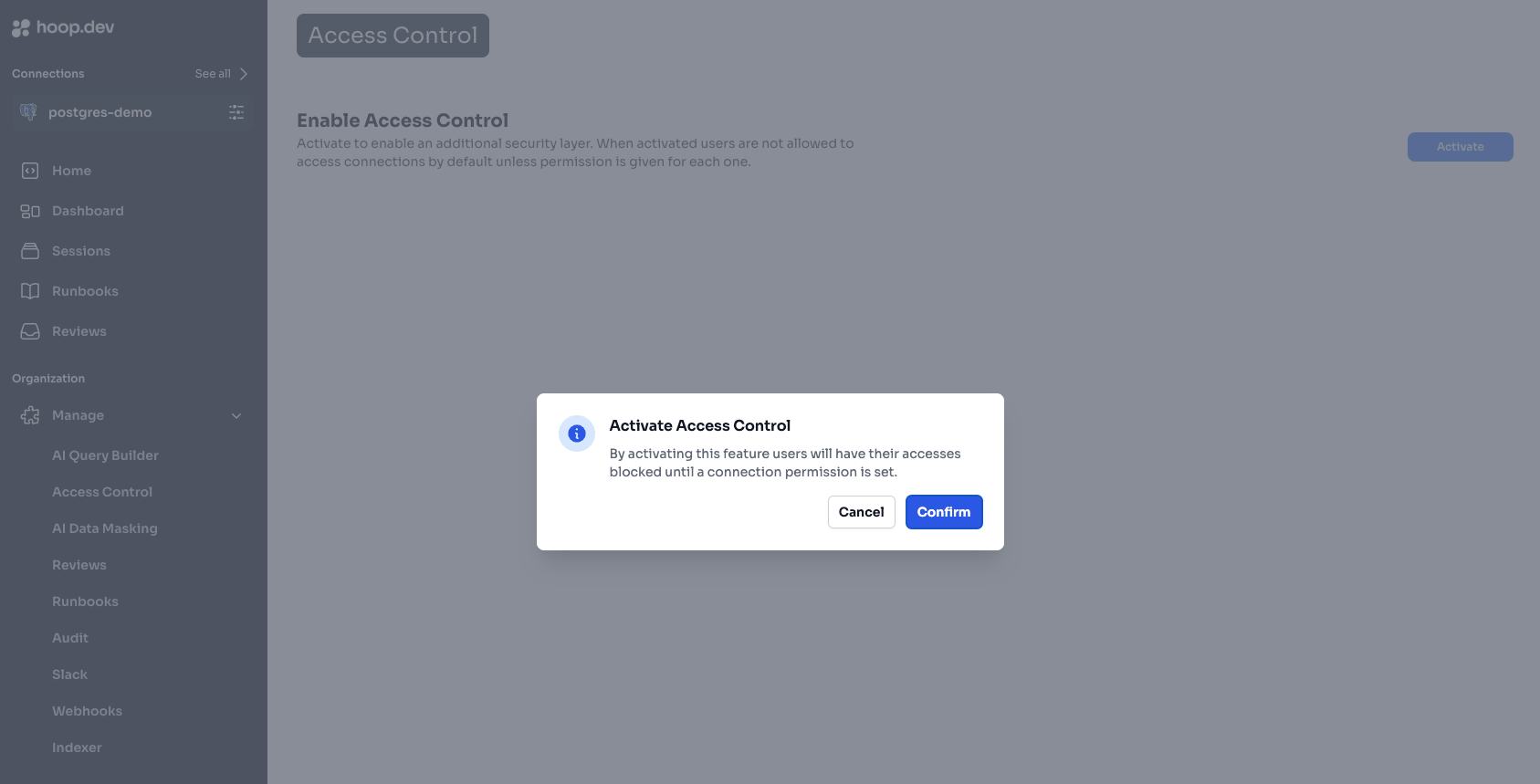
- Users without group assignments will lose access
- You’ll need to configure each resource role individually
- Changes take effect immediately
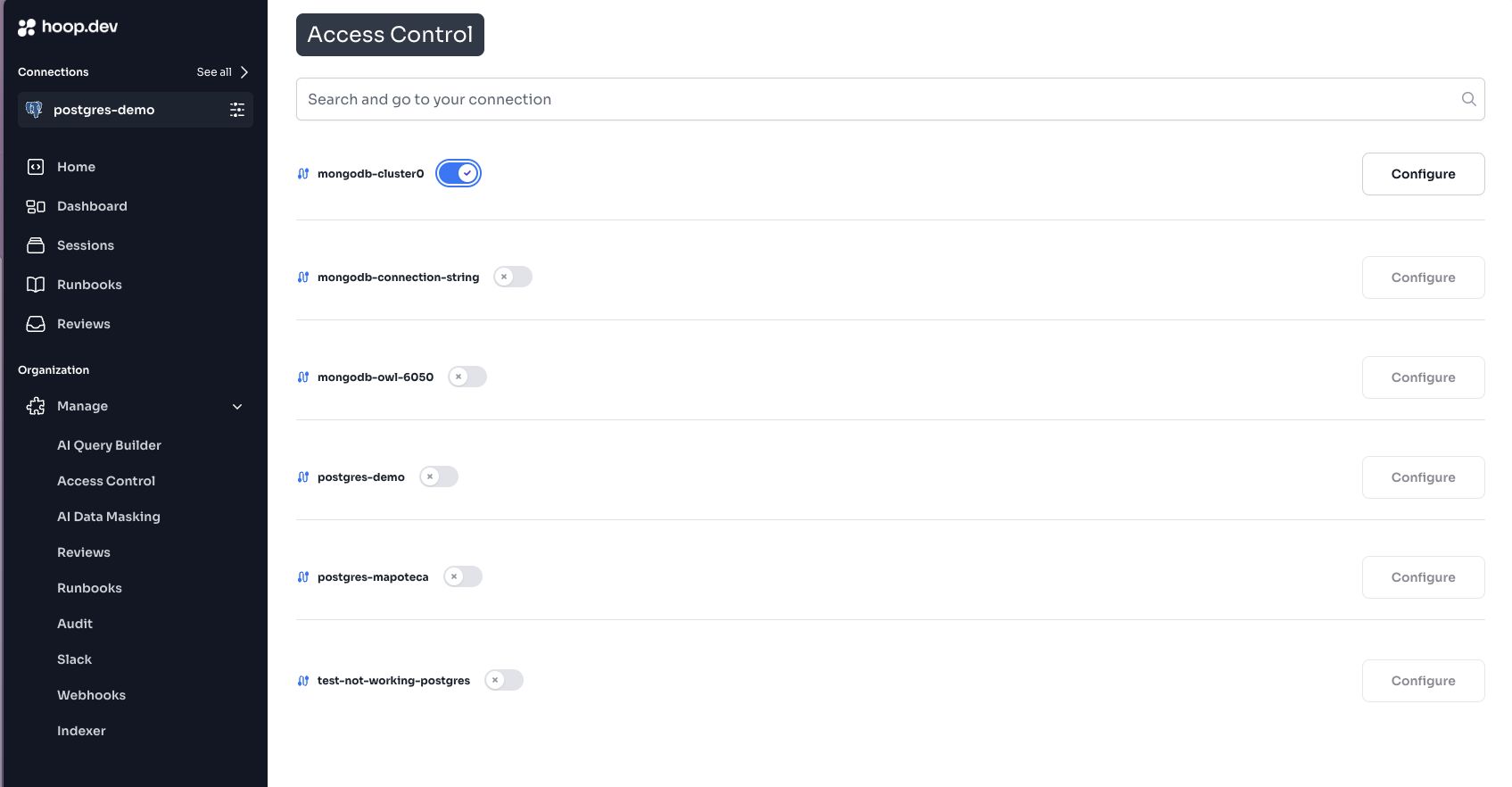
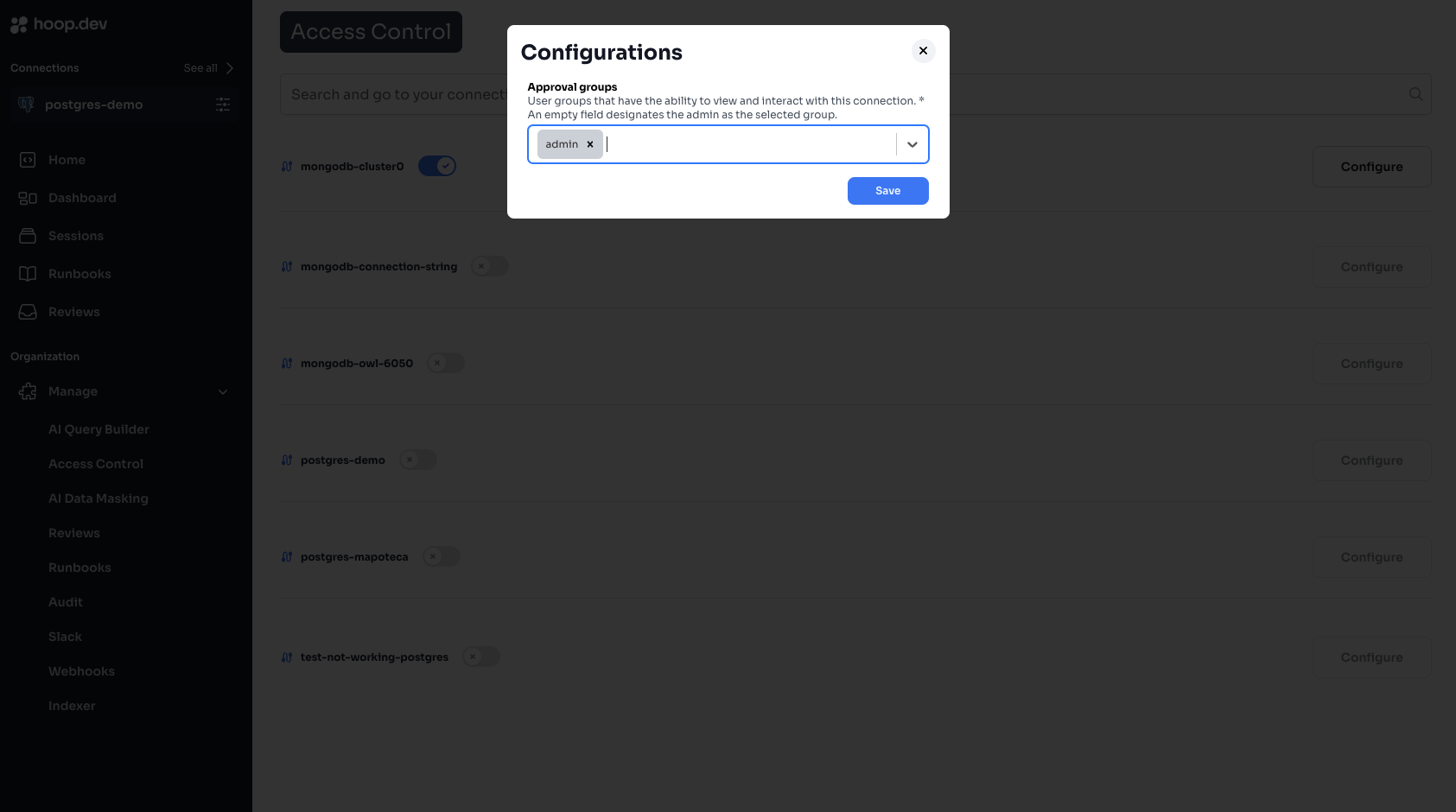
Step 2: Configure Resource Roles
After activation, configure access for each resource role:Group Management
Creating Groups
Groups can be created in two ways: Option A: Manual Creation (in Hoop)- Go to Manage > Users & Groups
- Click the Groups tab
- Click Create Group
- Enter a group name (e.g.,
prod-access,analytics-team) - Add users to the group
- Configure your IdP to include
groupsclaim in the ID token - Users’ groups are synced on each login
- See Identity Provider Configuration
Built-in Groups
| Group | Description | Permissions |
|---|---|---|
admin | Administrators | Full access to all resource roles and settings |
auditor | Audit access | Read-only access to sessions and logs |
Admin users bypass Access Control and can access all resource roles regardless of group configuration.
Group Naming Conventions
Recommended naming patterns:| Pattern | Example | Use Case |
|---|---|---|
| Environment | prod-access, staging-access | Environment-based access |
| Team | engineering, analytics, support | Team-based access |
| Role | dba, developer, viewer | Role-based access |
| Combined | prod-dba, staging-dev | Specific combinations |
Permission Types
Resource Role Visibility
When Access Control is enabled on a resource role:| User’s Groups | Resource Role Visibility |
|---|---|
| In allowed groups | Resource role is visible and accessible |
| Not in allowed groups | Resource role is hidden completely |
| Admin group | Always visible (bypasses Access Control) |
Combining with Access Requests
Access Control and Access Requests work together:| Access Control | Access Requests | Result |
|---|---|---|
| Allowed | Not enabled | Direct access |
| Allowed | JIT enabled | Must request time-based access |
| Allowed | Action enabled | Each command needs approval |
| Not allowed | Any | Resource role not visible |
Configuration Patterns
Pattern 1: Environment-Based
Separate access by environment:Pattern 2: Team-Based
Each team accesses their own resources:Pattern 3: Read/Write Separation
Create separate resource roles with different access levels:Pattern 4: Contractor Access
Limited access for external contractors:Identity Provider Integration
Syncing Groups from IdP
To automatically sync groups from your identity provider:-
Configure IdP to include groups claim:
In your IdP (Okta, Auth0, Azure AD, etc.), configure the OIDC application to include a
groupsclaim in the ID token. -
Set environment variables on gateway:
Or for custom claim names:
- Groups sync on login: When users log in, their groups are automatically synced from the IdP.
Provider-Specific Guides
Okta
Configure Okta group sync
Auth0
Configure Auth0 group sync
Azure AD
Configure Azure AD group sync
Configure Google Workspace groups
Auditing Access
Viewing User Permissions
To see what a user can access:- Go to Manage > Users
- Click on a user
- View their group memberships
- Cross-reference with resource role configurations
Access Logs
All access attempts are logged:- Go to Sessions
- Filter by user or resource role
- See successful connections and denied attempts
Exporting Access Report
Generate a report of who can access what:Troubleshooting
User Can’t See a Resource Role
Checklist:-
Is Access Control enabled on the resource role?
- Go to resource role settings
- Check if Access Control toggle is on
-
Is the user in an allowed group?
- Go to Manage > Users
- Check user’s group memberships
- Verify groups match resource role’s allowed groups
-
Has the user logged out and back in?
- Groups sync on login
- Have user log out and log in again
-
Is the IdP sending groups correctly?
- Check IdP configuration
- Verify
groupsclaim in ID token
User Sees Resource Role But Can’t Connect
This is likely NOT an Access Control issue. Check:- Access Requests: Is JIT or Action approval required?
- Guardrails: Are there blocking rules?
- Resource role status: Is the agent online?
Groups Not Syncing from IdP
Check:- IdP is configured to include
groupsclaim IDP_GROUPS_CLAIMenvironment variable is set correctly- User has groups assigned in the IdP
- Gateway was restarted after configuration
- Decode the ID token to verify
groupsclaim is present - Check gateway logs for group sync errors
Best Practices
Start Restrictive
Begin with minimal access and expand as needed
Use Groups, Not Users
Always assign access to groups, never individuals
Document Policies
Maintain a document of who should access what
Regular Reviews
Audit access quarterly
Before Enabling Access Control
- Inventory all resource roles
- Identify who needs access to each
- Create groups in IdP or Hoop
- Assign users to groups
- Document the access policy
- Test with a non-production resource role first
Quarterly Access Review
- Export current access configuration
- Review with team leads
- Remove departed employees
- Verify contractor access is time-limited
- Update documentation
Related
Access Control Overview
Learn Access Control concepts
Identity Providers
Configure SSO and group sync
Access Requests
Add approval workflows
Managing Access
User and group management in Web App