The Challenge of Infrastructure Access
Organizations face significant challenges when managing access to critical infrastructure:- Security risks from overly permissive access policies
- Productivity bottlenecks from complex approval workflows
- Compliance headaches due to inadequate audit trails
- Visibility gaps in understanding who accessed what and when
- Sensitive data exposure risks during access sessions
Our Solutions
Hoop.dev offers a range of features to help you secure your infrastructure and streamline access for developers, including:AI Data Masking
Zero-config DLP policies that automatically mask sensitive data in real-time at the protocol layer. Protect PII, credentials, and other sensitive information without requiring complex rule setup.
Learn more
Learn more
Reviews
Enable time-based access sessions or command-level reviews. Users request access or review while approvers guarantee security without sacrificing productivity.
Learn more
Learn more
Access Control
Define granular access policies determining which users or groups can access specific connections. Integrate with your existing identity provider to maintain consistent access governance.
Learn more
Learn more
Guardrails
Intelligent protection layer that automatically enforces access policies and prevents risky operations in real-time. Keep your infrastructure secure with smart command filtering and context-aware access.
Learn more
Learn more
Runbooks
Automate tasks with templated runbooks. Create, share, and execute procedures through a Git-based system, improving consistency and reducing errors.
Learn more
Learn more
Secrets Management
Securely integrate with most popular secrets management tools. Dynamically expand environment variables without exposing sensitive credentials.
Learn more
Learn more
Common Use Cases
Database Access Management
Database Access Management
Provide secure, audited access to databases while masking sensitive data. Enable developers to run queries without direct access to production credentials.
Secure Server Access Without VPN
Secure Server Access Without VPN
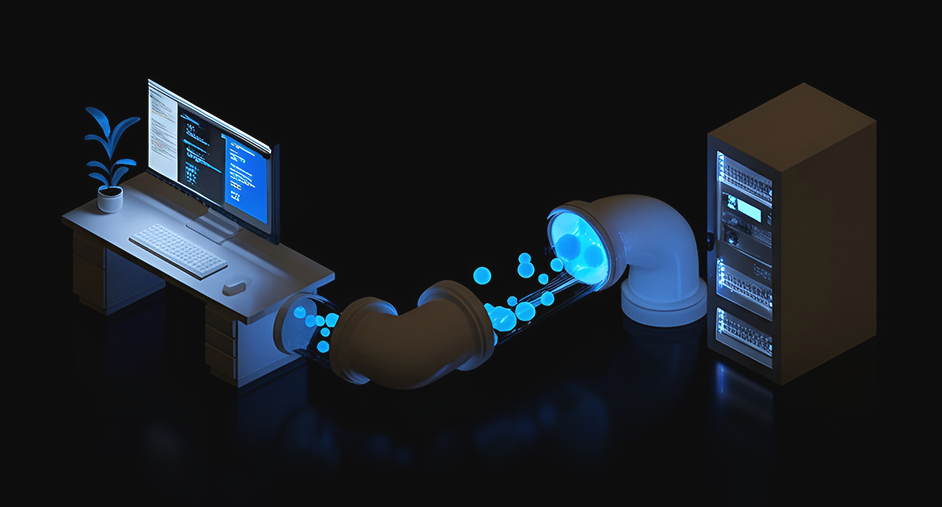
Eliminate the need for VPN by providing secure, authenticated access to servers and applications through Hoop.dev’s gateway.
Compliance & Auditing
Compliance & Auditing
Meet regulatory requirements with comprehensive session recordings, access logs, and data protection features that document who accessed what and when.
Developer Productivity
Developer Productivity
Streamline access to resources developers need while maintaining security guardrails that protect sensitive systems and data.
Getting Started
Hoop.dev is currently available in managed and self-hosted modes. Choose the option that best fits your needs:Managed Service
Get started with our managed platform. No complex setup required - just register and begin connecting your resources to secure your infrastructure access immediately.
Create free account
Create free account
Self-Hosted
Deploy Hoop.dev in your own infrastructure using Docker, Kubernetes, or AWS. Take full control over your environment setup with the same powerful features.
Go to deployment guide
Go to deployment guide