"Great! Now we can move to audit trails", he said with a smile. "Maybe your team should start building or hiring some engineers", I replied to the sec team lead. "Let's take this matter to the CTO", I continued while leaving the room to grab some water.
The meeting goal was to present the SSO solution requested by the sec team and finally get them off our back. The backlog of platform and developer experience items was paused for months. We had been prioritizing security features for a while since SOC2 re-certification was approaching.
Back in the meeting we setup a meeting with the CTO. I had a week to document the problems of the never-ending security backlog we had to implement. And it was in this process that I found a troubling issue: we were working on the wrong problem.
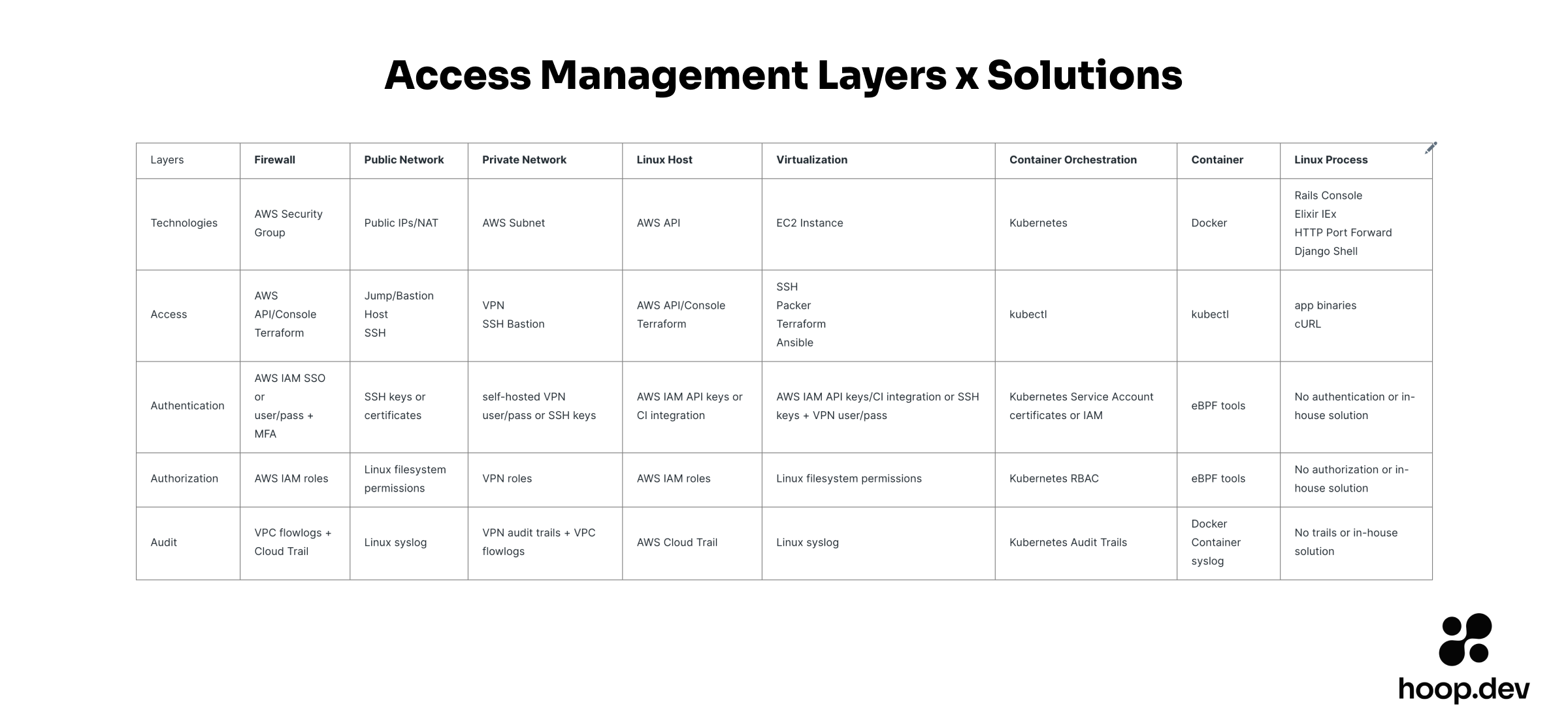
It is impossible to get table stakes of security features for all layers of today's stack
You are wasting your teams' time if working on individual security features.
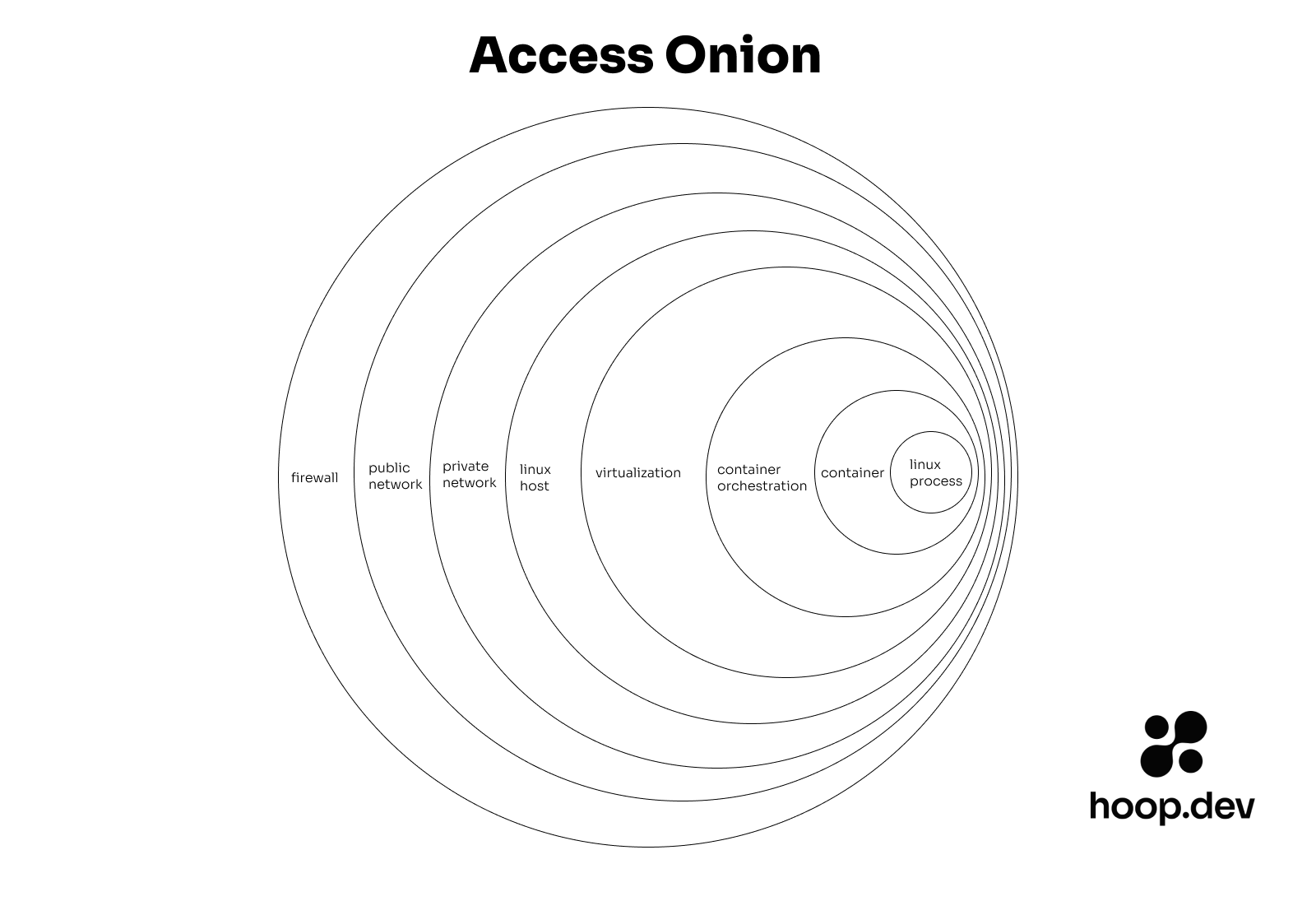
There are many invisible layers needing security work. Many times these layers are uncovered ad-hoc. Or worst: when they become problems. When this happen it is impossible to think strategically about the platform roadmap. Adding SSO to a VPN is one piece of a large puzzle. Then you have to add SSO to tools folks use with the VPN. Your database need SSO. Your messaging queue. And SSO is only one of the 4A security features. Realizing the size of this problem will reduce your work and enable you to work on higher impact projects.